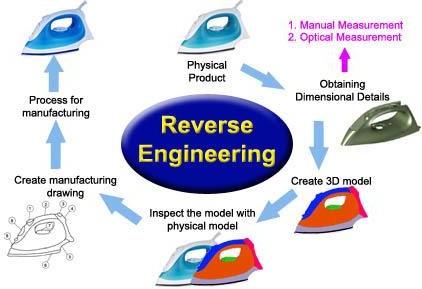
A product on a shelf, once opened and examined, becomes a map of someone else’s problem-solving: parts fitted together, materials chosen, compromises hidden beneath polished surfaces. Reverse engineering is the act of reading that map – disassembling, measuring, and decoding a rival’s creation – not to copy blindly but to understand the rationale, the trade-offs, and the sparks of ingenuity that produced it. In competitive markets this practice can be less about imitation and more about intelligence: a way to see into alternate design paths and borrow ideas that can be recombined into something new.
When companies treat competitors’ work as raw data rather than a finished verdict, they turn benchmarking into a creative engine. Reverse engineering exposes not only what works, but why it effectively works, where it falls short, and which constraints shaped its design. Those insights accelerate learning cycles, reveal opportunities for differentiation, and sometimes highlight unexpected technical or business innovations that would or else remain obscured. Viewed through this lens, reverse engineering becomes a disciplined curiosity - a mechanism for discovery that complements internal R&D rather than replacing it.
This article examines how reverse engineering, practiced responsibly and ethically, can propel innovation: from tactical improvements and cost efficiencies to conceptual leaps and new product platforms. We’ll explore methods for gleaning actionable insight, the organizational habits that turn findings into forward motion, and the legal and moral boundaries that shoudl guide the practice. The aim is not to glamorize copying, but to show how studying competition – up close and with care - can catalyze smarter, more creative responses in an ever-changing marketplace.
Reverse engineering with purpose: define learning objectives, metrics, and competitive hypotheses

Begin every analysis with razor-sharp intentions: decide what you must learn and why it matters to your roadmap. Translate vague curiosity into specific learning objectives – for example, whether a competitor’s onboarding flow improves activation, or if a premium feature drives retention for a particular segment. Frame each objective so it points to an actionable decision (build, copy, pivot, or ignore), and pair it with a primary signal you can measure. Use the competitor as a living lab: watch patterns, isolate variables, and convert observations into testable ideas rather than mimicry.
- Objective: Measure onboarding friction – Metric: time-to-first-value
- Objective: Validate premium demand – Metric: upgrade conversion rate
- Objective: Evaluate feature stickiness – Metric: 7-day retention for feature users
Anchor every insight with tight hypotheses and corresponding KPIs so your reverse engineering becomes a hypothesis-driven innovation engine. Design lightweight experiments that map a competitor behavior to your metric choices, then iterate quickly: if the data disproves a hypothesis, refine the assumption; if it supports it, scale the experiment into a product bet. This discipline turns competitive spying into strategic learning-controlled, measurable, and repeatable-so your team can prioritize ideas that move the business needle instead of chasing surface-level features.
| Objective | Metric | Competitive Hypothesis |
|---|---|---|
| Faster activation | Time-to-first-value | Streamlined onboarding reduces churn 15% |
| Monetization fit | Upgrade conversion | Tiered features convert mid-market users |
| Feature loyalty | 7-day retention | In-app guidance increases repeat use |
Structured teardown techniques and tools: hardware, software, and user experience methods to extract actionable data
When you pull a competing product apart,do it with intention: combine physical inspection,code excavation and human-observation to reveal design choices that matter. Start with hardware probing (high-torque drivers, microscopes, thermal cameras), pair it with firmware extraction (JTAG, flash readers, binwalk) and close the loop with behavioral testing (traffic sniffers, emulators, crash fuzzers). Practical steps you can reuse include:
- Disassembly kit - torque bits, spudgers, magnification
- Signal capture – logic analyzers, oscilloscopes, packet captures
- Binary tools – disassemblers, decompilers, dependency explorers
- UX observation – task scripts, think-aloud sessions, heatmaps
convert artifacts into decisions by applying a fast, evidence-driven loop: triage anomalies, form hypotheses, prototype solutions and measure impact. below is a compact playbook mapping common findings to quick validation tools – use it to prioritize experiments and embed competitive intelligence into roadmaps.
| Insight Type | Quick Win Tool | Result |
|---|---|---|
| Performance bottleneck | Profiler & benchmark | Targeted optimization |
| Hidden feature behavior | A/B prototype | Market-fit test |
| Confusing UX flow | Usability session & metrics | Clearer interaction model |
Ethical and legal guardrails for competitor analysis: compliance checklists and risk mitigation steps

Seen through a pragmatic lens, legal and ethical guardrails are not roadblocks but a design brief for responsible ingenuity. Start with a compliance checklist that becomes part of your sprint planning: verify terms of service and robots.txt,confirm copyright and licensing boundaries,run a privacy impact review for any scraped data,and respect employment and contractor NDAs. Keep these essentials in focus as you reverse engineer – they define what you can learn, how you record it, and which techniques require a clean-room approach to avoid intellectual property entanglements.
- Confirm ToS & crawling rules
- Perform copyright & trade-secret screening
- Minimize processing of personal data
- Use clean-room teams for reimplementation
- Log activities for auditability
| Risk | Mitigation |
|---|---|
| Copyright claims | Clean-room dev + counsel review |
| Trade secret exposure | Segregated teams + NDAs |
| Privacy breach | Data minimization + DPIA |
Operationalize risk mitigation by turning principles into habits: document every data source and decision, limit scope to non-proprietary behaviors, and build a repeatable clean‑room process for translating observed behavior into original implementations. Couple those practices with routine legal reviews and auditable logs so every insight you extract is defensible and every innovation you ship amplifies trust as much as it amplifies capability.
Mapping findings to strategic opportunities: feature gap analysis, customer value mapping, and prioritization frameworks

Peeling back competitors’ products turns scattered clues into a strategic map: feature gaps become signals of unmet customer desire, and usage patterns reveal where convenience or trust is missing. Translate those signals into concrete levers by building a feature gap inventory, then layer a customer value map that ties each gap to emotional and functional outcomes (time saved, confidence, delight). Use lightweight synthesis rituals-10-minute affinity sorting, a one-page value canvas, or a quick Kano sketch-to move from noise to insight. Frameworks that reliably do the heavy lifting include:
- RICE (Reach, Impact, Confidence, Effort) – for scoring potential outcomes;
- Kano - to separate delighters from must-haves;
- Value vs. Effort - to visualize low-effort, high-value quick wins;
- Prospect Solution Tree – to keep solutions tied to customer problems.
these tools turn reverse-engineering data into a palette of strategic opportunities you can test and iterate on.
With a short, defensible prioritization step you stop guessing and start allocating resources to hypothesis-driven bets. The table below sketches how a few discovered gaps might be mapped and prioritized for a next sprint, using simple verdicts that product teams can act on immediately.
| Feature gap | Customer value | Effort | Priority |
|---|---|---|---|
| Offline access | reliability in low-connectivity | Medium | High |
| Personalized onboarding | Faster time-to-value | Low | Quick Win |
| Advanced analytics | Deeper decision support | High | Medium |
- Run a short experiment for each high-priority item (prototype → A/B → learn);
- Translate validated wins into roadmap epics with clear success metrics;
- Communicate trade-offs using the selected framework so stakeholders see the logic behind choices.
By connecting reverse-engineering insights to clear value and prioritized execution,you convert imitation into a disciplined source of innovation.
Turning insights into experiments: designing prototypes, split tests, and implementation milestones
When a competitor’s product reveals a clever tweak, the real work begins not with imitation but with translation: distill that feature into a clear hypothesis and sketch a lean prototype that tests the underlying user benefit.Start by building micro-prototypes that capture the core interaction,then define the single most vital outcome you expect to move – be it conversion,engagement,or retention. Use quick experiments to validate assumptions before scaling; practical steps include:
- Prototype fast - wireframes or clickable mocks within 48 hours
- Isolate variables – change one element per test
- Choose leading metrics – pick the signal that correlates to long-term value
- Recruit audiences – internal beta,segmented cohorts,or paid panels
This approach converts inspiration into disciplined inquiry,so each learnings becomes an asset rather than a copy.
Designing split tests and implementation milestones turns those validated prototypes into product outcomes: schedule short A/B windows, define success thresholds, and plan safe rollouts with rollback criteria. Frame each milestone as a small wager – an intentional, measurable change – and align teams around the metric that matters. Typical milestone cadence might look like:
- Sprint 0 – hypothesis, acceptance criteria, and prototype
- Sprint 1 – live A/B test against control
- Sprint 2 – analyze results, iterate, or expand
- Release – staged rollout with monitoring and fallback
By treating competitor insights as a pipeline of testable experiments and staging implementation into clear milestones, you reduce risk, accelerate learning, and turn reverse engineering into a repeatable innovation engine.
Institutionalizing competitive reverse engineering: continuous monitoring,knowledge sharing,and IP aware innovation playbooks

Turn competitive reverse engineering into a repeatable muscle by embedding it into everyday workflows: equip teams with continuous monitoring pipelines that flag design shifts, and codify findings into shared libraries so insights don’t vanish with the next sprint. Practical steps to adopt now include:
- Automated feeds from market scans and component registries
- Teardown templates that standardize evaluation and minimize reinventing the wheel
- IP-aware playbooks that map observed features to safe reuse strategies
These elements make discovery tactical rather than accidental, so engineering roadmaps and product strategy are constantly fed by what rivals reveal.
Institutionalization also demands governance and storytelling: training programs, cross-functional reviews and a simple scoreboard keep momentum and compliance aligned. The following snapshot shows a practical division of responsibilities and short, measurable signals to watch:
| Role | Quick KPI |
|---|---|
| Product Intelligence | New insights/week |
| Engineering | Prototypes inspired by RE |
| Legal & Compliance | IP clearance turnaround |
Pair these governance items with regular “lessons learned” sessions and a lightweight, IP-informed innovation playbook so teams can turn reverse-engineered signals into product differentiation-fast, repeatable, and defensible.
The Way Forward
Reverse engineering a competitor’s product is less an act of copying than a method of conversation - one that translates someone else’s choices into insights about materials, priorities and problem‑solving paths. When approached with curiosity, restraint and clear legal and ethical boundaries, it reveals not just what works, but why it effectively works, and where gaps invite new thinking. The real value comes from folding those lessons into your own design language and strategy, turning borrowed understanding into distinct solutions that address unmet needs. Done well, this practice accelerates learning cycles, sharpens hypotheses and surfaces opportunities that pure speculation would miss. As with any tool, its potential depends on how intentionally it is used: as a shortcut to imitation or as fuel for original progress. Either way,reverse engineering reminds innovators that the fastest route forward is often paved by understanding the ground already trodden – then choosing a different path.